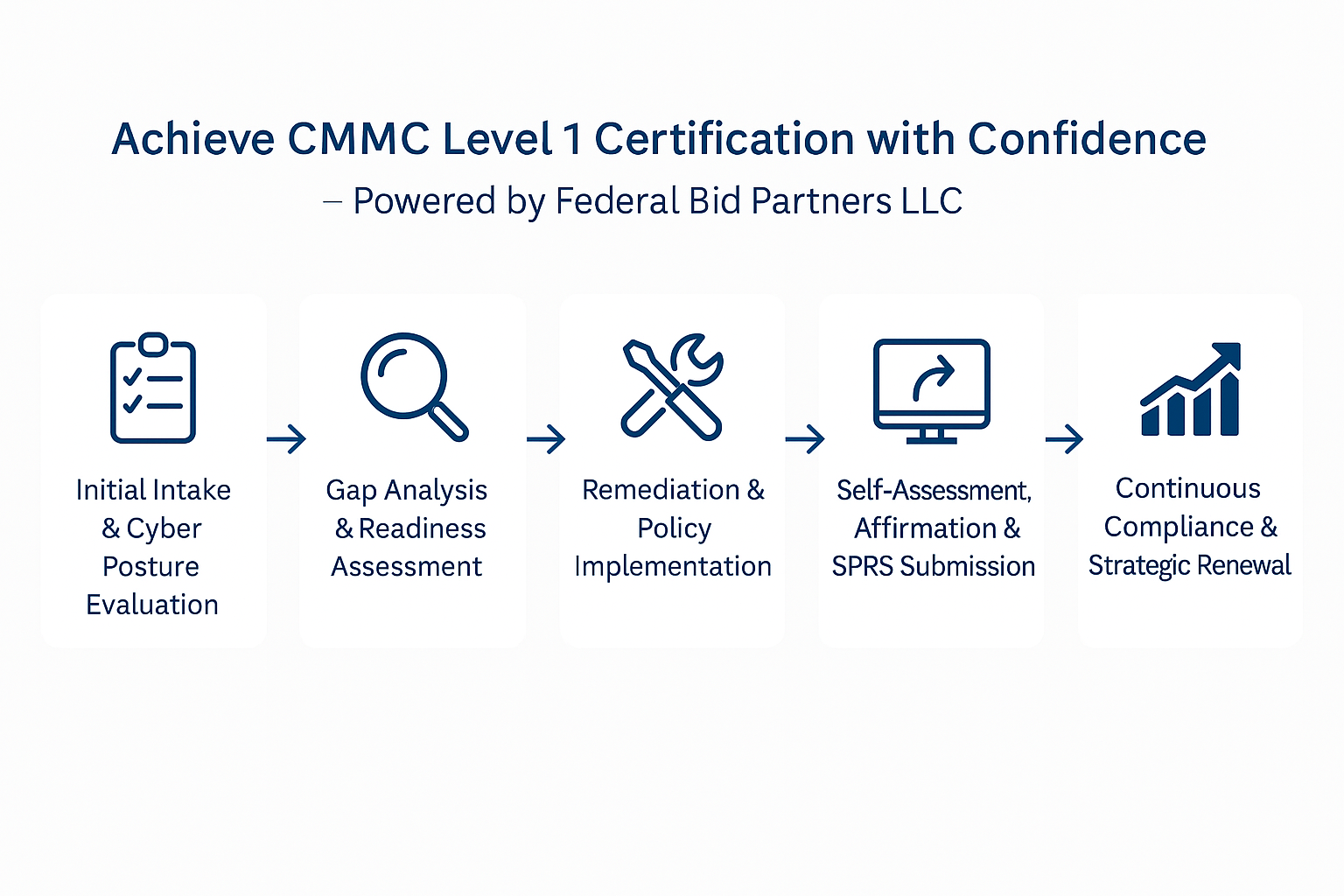
Achieve CMMC Level 1 Certification with Confidence – Powered by Federal Bid Partners LLC
To engage in contracts with the Department of Defense (DoD), contractors handling Federal Contract Information (FCI) must demonstrate basic cyber hygiene by achieving Cybersecurity Maturity Model Certification (CMMC) Level 1. This certification verifies that your organization follows 17 essential security practices aligned with FAR 52.204-21, ensuring foundational protection of sensitive data.
At Federal Bid Partners LLC, we provide end-to-end certification services to ensure your compliance with CMMC Level 1—whether you're preparing to compete or already awarded a DoD contract. Our proven methodology supports businesses of all sizes with policy development, gap remediation, self-assessment submission, and ongoing compliance strategies.
Orientation & Information Gathering
Orientation & Information Gathering
The first phase of the certification process begins with a full discovery session and environment mapping. We begin by assessing the nature of your business and determining whether your organization handles Federal Contract Information (FCI) in any form. This discovery process helps us define your CMMC scope — which systems, people, and processes must be brought into alignment with CMMC Level 1 practices.
You will complete a structured intake form where we gather critical information about your organization’s size, IT architecture, security maturity, existing policies, use of contractors, and the types of contracts you are pursuing or maintaining. We also review your current approach to access control, user authentication, physical security, device management, and data sharing.
This evaluation phase is where we determine if CMMC Level 1 is appropriate for your business goals or if your environment hints at future Level 2 needs. We'll identify which systems must fall within the certification boundary and explain how that boundary is defined from a NIST and DoD compliance perspective. If necessary, we also provide a plain-language explanation of CMMC terminology so your stakeholders are on the same page.
The deliverable from this phase is a strategic readiness summary: a tailored snapshot of your current security posture, where gaps are likely to exist, and what needs to be addressed before moving forward with compliance documentation.
Mapping Your Current Posture to CMMC Requirements
Mapping Your Current Posture to CMMC Requirements
Once your environment and information flows are mapped, we begin the formal gap analysis. This is a control-by-control assessment, where we compare your existing cybersecurity safeguards against the 17 security requirements outlined by CMMC Level 1. These practices are derived from NIST SP 800-171 Rev. 2 and are focused on protecting FCI through basic cyber hygiene.
This evaluation is both technical and procedural. We examine whether user access is limited on a need-to-know basis, if multi-factor authentication is implemented, how removable media is handled, and whether unauthorized physical access to systems is possible. Every control is assessed against a checklist based on the NIST 800-171A audit methodology to ensure defensibility.
Once our consultants complete this assessment, we develop a detailed gap report. This document outlines each unmet requirement, why it is out of scope or insufficient, and exactly what needs to be done to bring the control into compliance. We also include a maturity rating to illustrate how far off each control is from where it needs to be, along with an estimated remediation timeline.
You’ll also receive your unofficial CMMC readiness score and a projected SPRS (Supplier Performance Risk System) self-assessment score. At this stage, we also begin drafting your Plan of Action and Milestones (POA&M), which will list each unresolved issue and track your remediation progress.
Corrective Action & Control Implementation
Corrective Action & Control Implementation
After the gap assessment is complete, we transition into active remediation. This is where we close the gaps between your current security posture and the requirements for CMMC Level 1 certification. Our team supports both technical and administrative remediation, ensuring that the 17 required practices are not just understood, but implemented and enforceable.
On the technical side, we guide your team through adjustments to access control mechanisms, such as removing shared accounts, applying least privilege policies, and implementing time-based logouts. We advise on simple, cost-effective methods for implementing multi-factor authentication, secure log storage, and automated screen lockouts. Our recommendations are customized to your existing tools and systems—no unnecessary software or vendor lock-in.
Administratively, we help you draft the policies that must be in place for auditors to validate your controls. This includes a customized System Security Plan (SSP), detailing your infrastructure, boundary, and specific control implementations. We provide policy templates tailored to CMMC Level 1 expectations, including access control, physical security, incident reporting, and removable media handling.
All documentation is aligned with DoD expectations for traceability, version control, and audit-readiness. This phase is also where we train your staff on maintaining compliant behavior, such as secure email practices, badge requirements, or clean desk policies. Once these changes are implemented, we conduct a post-remediation review to verify that your new state is compliant and sustainable.
Submission & Official Compliance Entry
Submission & Official Compliance Entry
With your technical and administrative controls in place, your organization is ready to complete the official self-assessment. Unlike CMMC Level 2 and above, Level 1 allows for self-assessment accompanied by a senior official affirmation statement. However, the information submitted must be accurate, complete, and defensible in the event of a DoD inquiry or audit.
We guide your leadership team in preparing this self-assessment using the DoD’s standardized scoring methodology (based on NIST 800-171). You’ll receive your final SSP and POA&M files, which must be retained for a minimum of three years and made available upon DoD request.
Next, we walk your organization step-by-step through the Supplier Performance Risk System (SPRS) account setup process. This includes requesting access via PIEE (Procurement Integrated Enterprise Environment), validating the correct Entity ID (SAM registration), and submitting your score securely.
We assist in drafting your executive affirmation letter, which must be signed by a senior official within your organization, attesting to the accuracy of the self-assessment. Once everything is submitted and your SPRS entry is confirmed, you will be officially marked as CMMC Level 1 compliant.
This phase includes a final compliance package for your internal records, complete with your SSP, POA&M, system boundary diagram, training logs, and a compliance certificate issued by Federal Bid Partners LLC.
Sustaining Compliance & Staying Competitive
Sustaining Compliance & Staying Competitive
Achieving CMMC Level 1 certification is not a one-time activity—it must be reaffirmed annually, and your practices must evolve alongside threats and federal updates. That’s why Federal Bid Partners offers post-certification services to help your organization maintain compliance long-term.
We offer optional quarterly or semi-annual check-ins where we review your control implementation status, validate policy adherence, and update any documentation as needed. If an incident occurs or a significant change is made to your IT infrastructure, we assist in revising your SSP and POA&M accordingly.
Our team monitors changes from DoD, NIST, and the CMMC-AB to ensure you stay ahead of emerging updates. If CMMC Level 2 becomes a requirement in your future contracts, we’ll help you plan a seamless transition to that higher level of certification.
To reinforce your credibility with clients and primes, we provide you with a CMMC Level 1 Compliant Badge for use on your website, capability statements, and proposal submissions. We also maintain your SPRS score documentation in case of an audit or revalidation request from an agency.
By sustaining your compliance with proactive support and strategic foresight, you not only remain eligible for DoD work—you stay competitive in a tightening cyber landscape.
Choose Your Plan
Sign up for the plan that fits your needs perfectly.
| $1,995 (2 Weeks) | $2,495 (1 Week Expedited) | |
|---|---|---|
| Full gap analysis | ✔ | ✔ |
| Remediation guidance | ✔ | ✔ |
| Self-assessment prep | ✔ | ✔ |
| SSP + documentation support | ✔ | ✔ |
| Ongoing email support | ✔ | ✔ |
| Priority scheduling | 🅧 | ✔ |
| Dedicated compliance team | 🅧 | ✔ |
| Advanced scanning tools | 🅧 | ✔ |
Fast Response and Easy to Follow Steps
We will provide you with a comprehensive list of everything needed to create your proposal. This may include signing a few documents, but we handle the rest, such as filling in your information (e.g., address, name, CAGE code, etc.). We ensure that you understand every aspect of the process. If you have any questions or need assistance, we are always ready to schedule a meeting or a call to help you.
Flexible Payment Schedule
We understand that new businesses are still in the startup phase and may not have the necessary funds to purchase our services. Therefore, we offer small businesses the opportunity to negotiate a fair price or payment plan, ensuring you can still maintain the budget needed to run your company.
Don't have a business yet? No problem.
We understand that starting a business can be challenging. Instead of paying another service to establish your business, we will file the necessary documents for you. Depending on your state, you will have your EIN within 2-3 business days, with no rush options and a flat rate. We will then create a website for you with email access (e.g., yourname@yourcompany.com) and register you on SAM.gov to enable your government contracting capabilities. Additionally, we can sign you up with popular vendors to pursue single-source procurement contracts, which are ideal for new businesses with no past performance. These contracts typically range from $10,000 to $150,000.
MENU
GET IN TOUCH
(813) 596-8866
contact@federalbidpartners.com
1704 Llano St
Ste B-1107
Santa Fe, NM 87505 USA
STAY CONNECTED
Join our newsletter and find out more
Contact Us
We will get back to you as soon as possible
Please try again later